Full disclosure: I completely stole this issue from a JDEList thread and the solution from user ice_cube210 (Tonio Thomas).
Problem Presentation
The problem manifests as a prompt in the browser every time a user opens a PDF from Work with Submitted Jobs (WSJ) asking what they want to do with the file:
 |
| Internet Explorer 8 |
 |
| Firefox 6 |
This gets old really fast. Users generally want to open the file.
Background
The root of the problem, as mentioned above, is how a PDF is delivered to the browser. PDF's can be sent to a web browser as either a file/attachment or inline as defined by the "content-disposition" HTTP header. When a web server sends a PDF to a browser the content-disposition header is set to either "attachment" or "inline" or possibly not set at all. The value of the content-disposition header tells the browser how to handle the content as defined in the RFC's rfc2183-in-http and rfc2183. If the header is
content-disposition: attachment; the browser will enter the "Save as..." dialog. Use of the content-disposition: inline; header or the absence of a content-disposition HTTP header will cause the browser to use default processing to handle the content. From this point it is up to the browser to determine how to process the PDF. For Internet Explorer 8 default processing means opening the PDF in the browser's embedded PDF viewer and for Firefox 6, a separate PDF viewer (although this behavior can be changed).EnterpriseOne Behavior
By default, when a user selects "View PDF" in WSJ EnterpriseOne sends the PDF as a file, using the
content-disposition: attachment; header. This causes the browser to enter the "Save as..." dialog as stipulated by rfc2183-in-http. The end user must then choose to either open or save the file. Choosing Firefox's "Do this automatically for files like this from now on" seems to be forever broken so is of no help.For the really geeky here's what the HTTP headers look like for the default E1 behavior:
HTTP/1.1 200 OK
Date: Wed, 21 Sep 2011 18:19:00 GMT
Server: IBM_HTTP_Server
Content-Disposition: attachment; filename =R0006P_XJDE0001_428652_PDF.pdf
Content-Length: 762280
Keep-Alive: timeout=10, max=99
Connection: Keep-Alive
Content-Type: application/pdf
Content-Language: en-US
Note the content-disposition header, with filename parameter.
Workaround/Solution
From Tools Release 8.98 on there has been an option to present PDF's in a manner that will automatically open in the user's browser. The setting is the "UBEContentDisposition" parameter in the [OWWEB] section of the JAS.INI and can be easily changed in Server Manager in the Web Runtime configuration for the JAS server as described here.
At first I thought Oracle had used the
content-disposition: inline; header but examination of the HTTP headers shows that once the setting is changed, the content-disposition header is simply removed.
HTTP/1.1 200 OK
Date: Wed, 21 Sep 2011 18:20:44 GMT
Server: IBM_HTTP_Server
Content-Length: 762280
Keep-Alive: timeout=10, max=88
Connection: Keep-Alive
Content-Type: application/pdf
Content-Language: en-US
I suppose that will work. The RFC allows for no content-disposition header. The absence of the header will cause the browser to use the default method of presentation and we get the desired behavior - automatically opening PDF's. I'd much rather see the
content-disposition: inline; header and have Oracle also use the Disposition Parameter: 'Filename' to give us a real filename to use when saving the file from Acrobat Reader (see below).Issues with Workaround
An issue with the fix may preclude some customers from using this workaround - when UBEContentDisposition is set to True (the default) and the PDF is sent as an attachment, the UBE name (R0006P_XJDE0001_429031_PDF.pdf) is sent to the browser/Acrobat Viewer and allows one to save the file with the original EnterpriseOne UBE name:
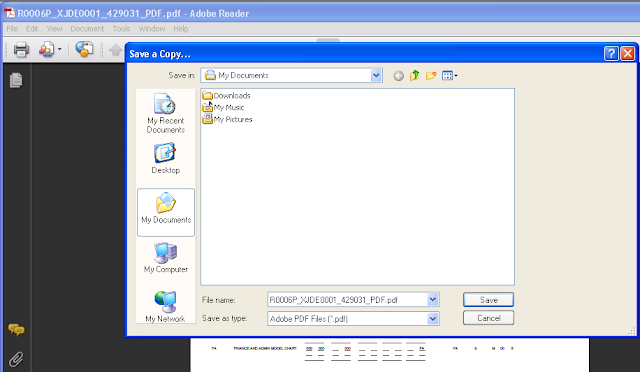 |
| Original UBE Name |
When using the workaround and setting UBEContentDisposition to false, a generic PDF name (com.jdedwards.jas.pdf) is passed in:
 |
| Generic Name |
This causes a problem when one wishes to save the PDF using the original UBE name for reference. You can always name the PDF whatever you like but it is darn convenient to have the report name passed in. Whether the naming issue is important enough to keep you from changing how PDF's are handled in the browser is an internal organizational issue. We should be able to pass in real UBE names using the
content-disposition: inline; header with the 'Filename' parameter but the smart folks at Oracle probably know something I don't. I've suggested it and we'll see.This is a very handy setting to change. Anything that makes end users' work easier and more efficient is worth doing.


 Email
Email Twitter
Twitter